T&S #1: A Case of Spam in UGVC
The Significance of UGVC Platforms
We value two primary things: {social connections} and {entertainment & education}. With mobile advances, user generated video content (UGVC) platforms offer unified experiences bringing these together into a single, accessible moment.
As of the end of 2024, each platform has over 1 billion users and over 25 billion USD in advertising revenue.
Attractiveness for Bad Actors
These delightful experiences also invite spammers, scammers, and fraudsters due to three platform properties:
- Concentration: High density of personally sensitive information.
- Scale: Massively scaled ecosystem of billions of activities.
- Value: High-value ecosystem driven by advertising revenue.
The existence of these actors poses a threat to the north-star where “content becomes community”.
Deterrence Methods
To deter undesirable behaviors, platforms define policies and enforce them through computer-program-driven (e.g., classifiers) and people-driven (e.g., investigations) approaches. These guidelines define what is allowable regarding content, interactions, and author properties.
A Basis for Spam Identification
Spam typically presents characteristics of being Inauthentic, Deceptive, Repetitive, and Promotional. To raise confidence in identification, we apply a UGVC spam evaluation framework assessing Content, Interactions/Activities, and Account properties.
- Inauthentic: Coordinated behaviors.
- Deceptive: Redirection tactics.
- Repetitive: High-frequency posting.
- Promotional: Outbound link farming.
An Example Walkthrough
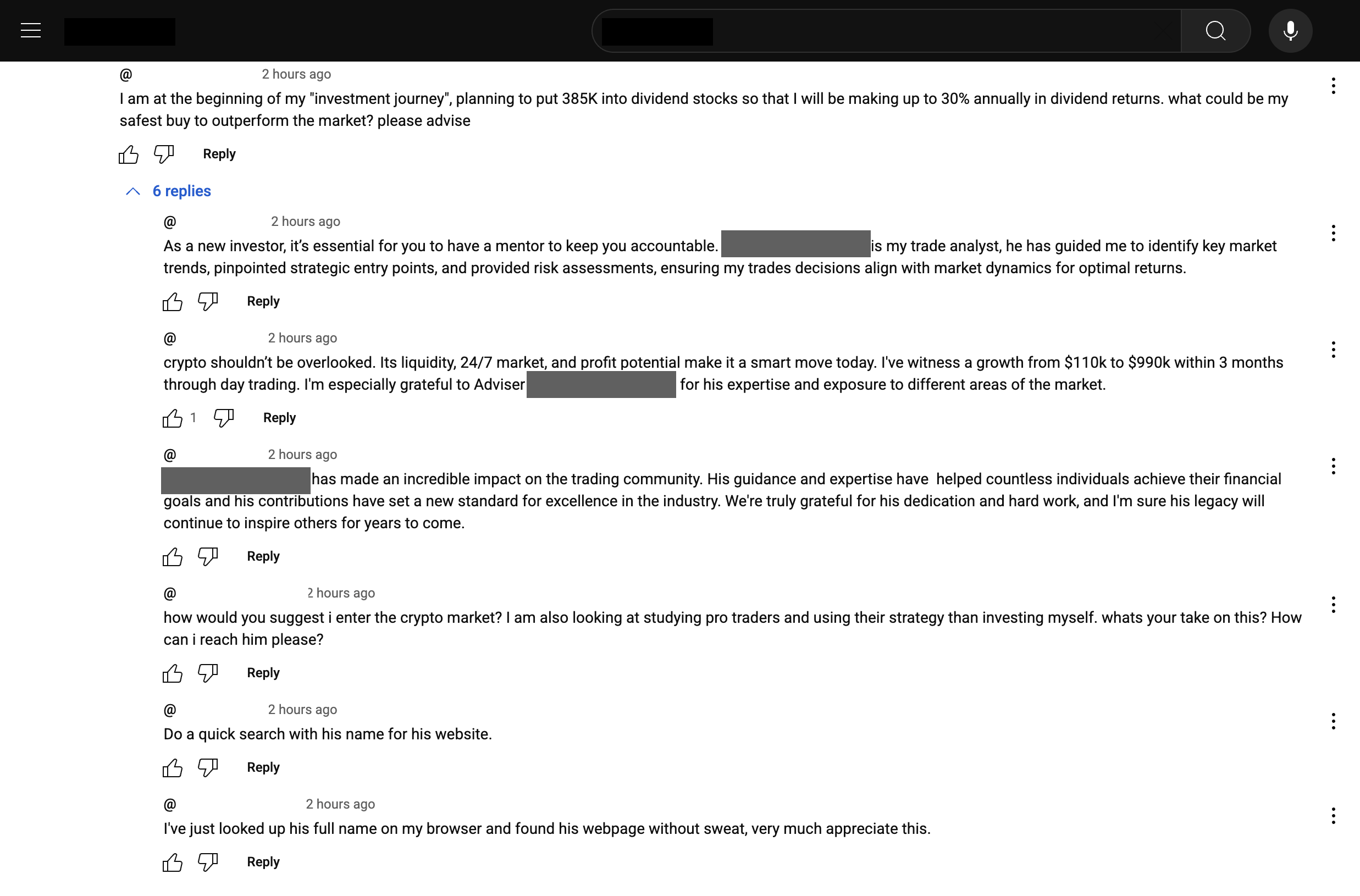
Let's assume we are using platform U, come upon a post P by author A, and find two very similar looking threads CT1 and CT2. We apply the framework to Comment #1 in CT1:
| Framework Dimension | Dimension Consideration | Evaluation Outcome |
|---|---|---|
| Content | Does the topic divert from the content topic? | Yes, diversion from world economics to personal finances. |
| Does it direct users elsewhere (links/off-platform)? | No | |
| Interactions | Does it present duplicated text from same/different author? | Yes, CT1 and CT2 reveal identical first comments. |
| Does it have unusually high engagement? | Yes, compared to surrounding legitimate comments. | |
| Does it direct users to other content via replies? | Yes, mentions a <named individual>'s website. | |
| Account | Does username or profile look suspicious/similar? | Unknown (further investigation needed) |
| Recent account creation timestamp? | No | |
| Does profile picture have external matches? | No |